Why This Comparison Matters
Disclosure: I built systemprompt.io. I will be as honest as I can about where Microsoft's toolkit is stronger and where it is not. You can judge whether I succeed.
On April 2, 2026, Microsoft open-sourced the Agent Governance Toolkit (AGT) under an MIT licence. A stateless policy engine for AI agents, with cryptographic identities, runtime isolation, compliance automation, and claimed coverage of all ten OWASP Top 10 for Agentic Applications risks. It shipped with support for Python, TypeScript, Rust, Go, and .NET. Over 9,500 tests. Integration with LangChain, CrewAI, Google ADK, and Microsoft's own Agent Framework.
This is genuinely significant. Microsoft entering the AI agent governance space validates what a growing number of CTOs already know: you cannot deploy autonomous AI agents without governance infrastructure. The question is no longer whether you need governance, but what kind.
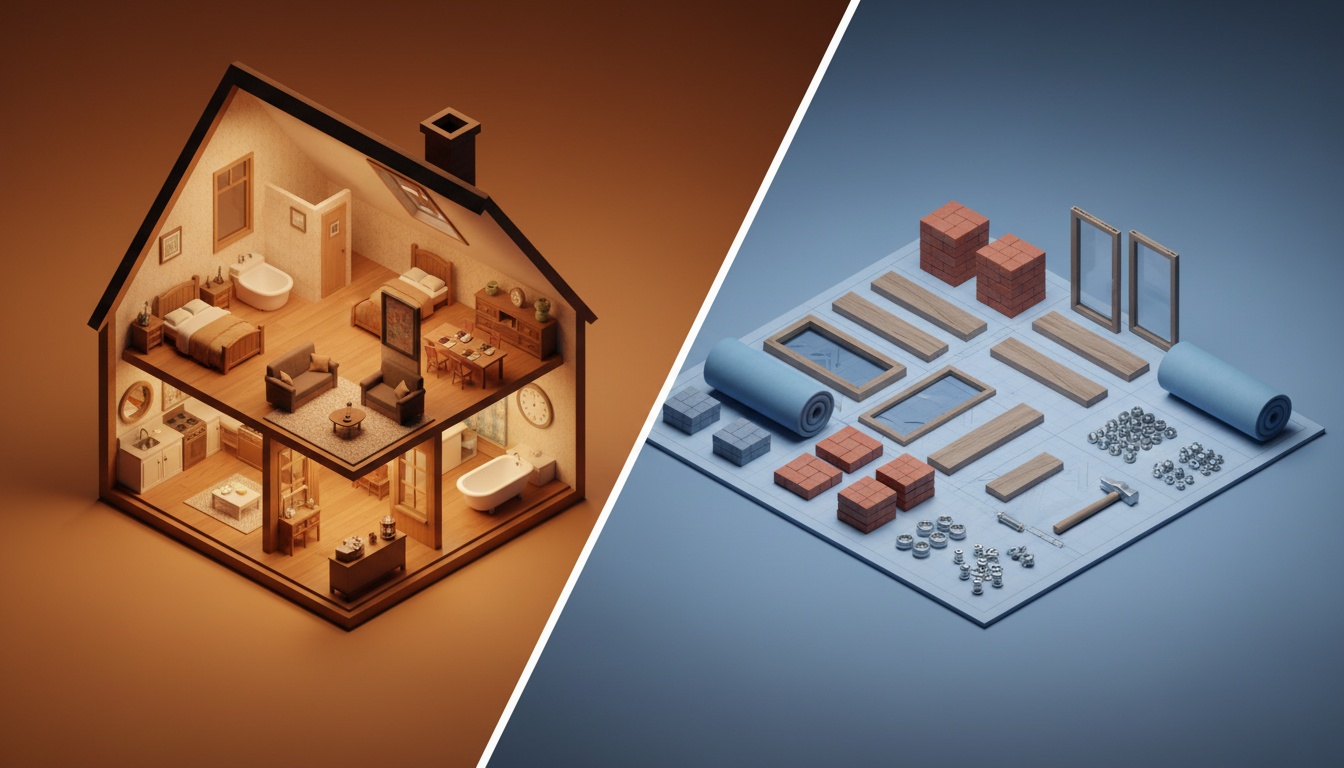
And that is where the distinction matters. Microsoft released a toolkit. What we built is a complete governance product. Those words sound interchangeable. They are not. A toolkit gives you components to assemble. A product gives you something to deploy. The engineering effort, the operational burden, and the time to production are fundamentally different. If you want the deeper argument for why governance needs to live on your own infrastructure regardless of which of these you pick, the self-hosted AI governance guide walks through the data residency, audit, and sovereignty requirements that rule out SaaS governance for most enterprises.
If you are a CTO evaluating how to govern AI agents across your organisation, this comparison will help you decide which approach fits your team, your timeline, and your constraints.
What Microsoft AGT Actually Is
I want to be thorough here because Microsoft's toolkit deserves a fair assessment. It is well-engineered, and dismissing it would be dishonest.
The Agent OS
The centrepiece of AGT is what Microsoft calls the Agent OS. It is a stateless policy engine that evaluates agent actions against governance policies at runtime. The performance claims are impressive: sub-millisecond latency with a p99 under 0.1ms. That means governance checks add effectively zero overhead to agent execution.
Stateless design is a deliberate architectural choice. Every policy evaluation is independent, which means you can scale horizontally without worrying about shared state or coordination between nodes. For organisations running thousands of concurrent agents, this matters.
Cryptographic Agent Identities
Every agent registered with AGT gets a cryptographic identity. This is not just a unique ID in a database. It is a verifiable credential that can be validated without contacting a central authority. In a multi-agent system where agents communicate with each other, this solves the trust problem: how does Agent A know that Agent B is who it claims to be?
This is a capability that most governance tools, including ours, do not currently offer at the protocol level. For organisations building agent-to-agent communication systems, cryptographic identity is genuinely valuable.
Runtime Isolation
AGT provides execution sandboxing for agents. Each agent runs in an isolated environment where its access to system resources, network, and data is controlled by policy. If an agent is compromised or behaves unexpectedly, the blast radius is contained.
The implementation uses container-level isolation on Azure Container Apps and AKS, with policy-defined boundaries. You define what an agent can access, and the runtime enforces it.
Compliance Automation
AGT includes policy templates for EU AI Act, HIPAA, and SOC 2 compliance. These are not just documentation. They are executable policies that the Agent OS enforces at runtime. If an agent attempts an action that violates a compliance policy, the action is blocked before it executes.
The compliance layer also generates audit evidence automatically. For organisations preparing for regulatory audits, this reduces the manual effort of proving that your AI systems comply with specific regulations.
Framework Agnostic
One of AGT's genuine strengths is breadth. It works with LangChain, CrewAI, Google ADK, and Microsoft's Agent Framework. If your organisation uses multiple agent frameworks (and many do), AGT provides a single governance layer across all of them.
The SDKs are available in Python, TypeScript, Rust, Go, and .NET (documented in the AGT GitHub repository). Whatever your team builds with, there is a native integration. This is a significant advantage for polyglot organisations.
OWASP Coverage
Microsoft claims coverage of all ten OWASP agentic AI risks, backed by 9,500+ tests. The project has active engagement with the OWASP community and is positioning itself as a reference implementation for agentic AI governance. This is ambitious. Covering all ten risks at a testing depth of nearly a thousand tests per risk suggests serious investment in the security surface.
What AGT Does Not Include
Here is where the distinction between toolkit and platform becomes concrete. AGT does not ship with:
- A web dashboard or admin interface
- User management or team provisioning
- A skill marketplace or plugin ecosystem
- Usage analytics or cost attribution
- SIEM integration (you build the event pipeline yourself)
- Knowledge management or content governance
- A deployment-ready binary (you assemble and deploy from components)
These are not criticisms. A toolkit is not supposed to include these things. But they are things your organisation will need, and someone on your team will need to build them.
What systemprompt.io Actually Is
Our approach to the same problem is different. Instead of providing components to assemble, the product ships as a complete governance stack that deploys from a single binary.
Single Binary, Full Stack
The entire platform ships as one 50MB Rust binary. PostgreSQL is the only external dependency. No Redis, no message queues, no container orchestration, no service mesh. You run the binary, point it at a database, and you have a governance platform.
This matters for two reasons. First, operational complexity is a real cost. Every additional service in your stack is another thing to monitor, patch, scale, and debug at 2am. Second, it makes air-gapped deployment straightforward. Copy the binary to a machine, configure the database connection, and the platform runs with zero internet access.
The Governance Pipeline
Where AGT has the Agent OS, the equivalent primitive here is the governance pipeline. It is a synchronous, four-layer enforcement chain that every AI interaction passes through before reaching the model.
Layer one is scope checking. Does this request fall within the boundaries defined for this agent or skill? Layer two is policy enforcement. Do the applicable governance policies permit this action? Layer three is content filtering. Does the request or response contain sensitive data, prohibited patterns, or policy violations? Layer four is audit logging. Every request, every decision, every policy evaluation is recorded with a full trace.
The pipeline is synchronous by design. Each layer must pass before the next executes. There is no "log and continue" mode where a policy violation is recorded but the action proceeds anyway. If a layer rejects the request, it stops.
RBAC and Department Scoping
The platform implements six tiers of role-based access control with department scoping. This goes beyond "admin, editor, viewer" roles. Each tier defines what AI capabilities are available, what data domains are accessible, which skills and agents can be used, and what governance policies apply.
Department scoping means that the marketing team's AI governance rules can differ from engineering's. The sales team can have access to CRM-connected agents that engineering cannot see. Each department operates under its own governance context while the organisation maintains a unified view.
Skill Marketplace and Plugin Management
The platform includes a full skill marketplace where organisations can publish, discover, and install governance-approved AI skills. Skills are not just prompts. They are governed capabilities with defined inputs, outputs, permissions, and audit requirements.
For organisations deploying Claude, this is how you standardise AI usage. Instead of every team member writing their own prompts and hoping for consistency, you publish approved skills through the marketplace. Everyone uses the same governed capabilities. If you are new to the concept of skills and how they relate to other extension types, the guide on skills vs agents vs MCP servers covers the decision framework.
Usage Analytics and Cost Attribution
Every AI interaction is tracked with cost attribution. You can see which team, which department, which agent, and which skill generated what cost. This is not an optional add-on. It is built into the platform because governance without cost visibility is incomplete.
For CTOs managing AI spend across an organisation, this is often the feature that closes the deal. Knowing that the marketing team spent a certain amount on content generation last month, while engineering spent a different amount on code review, is the difference between "AI is expensive" and "here is exactly where the money goes."
SIEM Integration
The platform outputs structured JSON events through three paths: direct database logging, stdout for container log aggregators, and webhook delivery for real-time SIEM ingestion. The events follow a consistent schema with trace IDs that correlate across the entire request lifecycle.
You do not need to build an event pipeline. You point your SIEM at one of the three output paths and the events flow. For organisations with existing security operations centres, this is the difference between weeks of integration work and an afternoon of configuration.
Audit Trail
The audit system captures 16 distinct event hooks across 5 trace points. Every governance decision, every policy evaluation, every scope check, every content filter result is recorded with full context. The trace follows a request from initial receipt through every governance layer to final response delivery.
This is designed for regulated environments where "we have logging" is not sufficient. Auditors want to see the complete decision chain: what was requested, what policies were evaluated, what decisions were made, and what was delivered.
MCP Native
The platform does not just support the Model Context Protocol. The governance pipeline IS the MCP transport layer. When Claude connects through MCP, every tool call, every resource request, and every prompt passes through the governance pipeline automatically.
This is a fundamentally different architecture from adding governance as a sidecar or middleware. There is no way to bypass the governance layer because the governance layer is the communication channel. For a deeper look at how MCP servers fit into a governed architecture, see the guide on MCP servers in production deployment.
Head-to-Head Comparison
| Dimension | Microsoft AGT | systemprompt.io |
|---|---|---|
| Product type | Open-source toolkit (components) | Complete governance platform |
| Deployment | Assemble from components on Azure (AKS, Container Apps) | Single 50MB binary + PostgreSQL |
| External dependencies | Azure services, container orchestration | PostgreSQL only |
| OWASP agentic AI coverage | All 10 risks claimed, 9,500+ tests | ASI01, ASI02, ASI03, ASI05, ASI09 (deep implementation) |
| Policy enforcement | Stateless Agent OS, sub-ms latency | Synchronous 4-layer pipeline |
| Identity model | Cryptographic agent identities | 6-tier RBAC with department scoping |
| Runtime isolation | Container-level sandboxing | Session isolation per agent/skill |
| SIEM integration | Build your own event pipeline | 3 output paths, structured JSON, ready to connect |
| Audit trail | Compliance evidence generation | 16 event hooks, 5-point trace, full decision chain |
| Dashboard | Not included | Built-in admin dashboard |
| User management | Not included | Full team provisioning and permissions |
| Skill management | Not included | Marketplace with governance controls |
| Cost tracking | Not included | Per-team, per-agent, per-skill attribution |
| MCP support | Not native (framework-agnostic via SDKs) | MCP-native (governance IS the transport) |
| Agent framework support | LangChain, CrewAI, Google ADK, MS Agent Framework | Claude-focused (MCP protocol) |
| Language SDKs | Python, TypeScript, Rust, Go, .NET | N/A (platform, not SDK) |
| Air-gap deployment | Possible but requires assembling offline dependencies | Copy binary + configure database |
| Open source model | MIT licence (fully open) | BSL 1.1 (source available, converts to open after change date) |
| Pricing | Free (Azure infrastructure costs apply) | Free evaluation, Enterprise licence (custom) |
| Time to production | Weeks to months (assembly, integration, custom UI) | Days (deploy binary, configure, onboard) |
Quick Decision Guide
| Choose Microsoft AGT if... | Choose systemprompt.io if... |
|---|---|
| You have a dedicated platform engineering team to assemble and maintain components | You need governance deployed in days, not months |
| Your organisation runs entirely on Azure infrastructure | You need a complete stack out of the box: dashboard, user management, cost tracking, SIEM integration |
| MIT licensing is a hard legal requirement | You need air-gapped deployment via a single binary |
| You are governing agents across multiple frameworks (LangChain, CrewAI, Google ADK, .NET) | Your agents run on Claude via MCP and governance needs to be the transport layer |
| You want to contribute to or audit an open-source governance project | You need skill and knowledge management built into the governance layer |
| Cryptographic agent-to-agent identity verification is a core requirement | You are a smaller team that cannot spare engineers for a multi-month build |
| You have months of runway for a custom build | You need something that works this week |
When to Choose Microsoft AGT
There are scenarios where Microsoft's toolkit is the better choice. Being honest about that matters more than winning an argument.
You have a platform engineering team
If your organisation has a dedicated platform or infrastructure team that builds internal tooling, AGT gives them excellent components to work with. The Agent OS is well-designed. The cryptographic identity system is genuinely novel. The compliance policy templates are a strong starting point. A competent platform team can assemble these into a governance system tailored to your exact requirements.
The key word is "team." This is not a weekend project. Building a dashboard, user management, analytics, and SIEM integration on top of AGT is real engineering work. But if you have the people and the timeline, the result will be exactly what you need, nothing more and nothing less.
You are in the Azure ecosystem
If your organisation already runs on Azure, AGT integrates naturally. AKS for orchestration, Azure Foundry Agent Service for agent management, Azure Container Apps for isolation. The operational patterns are familiar to your team. The billing is consolidated. The support channels are established.
Using a Microsoft toolkit on Microsoft infrastructure with Microsoft support is a reasonable default for Azure-native organisations.
You need MIT licensing
Our platform uses the Business Source Licence 1.1. AGT uses MIT. If your legal team requires fully permissive licensing with no restrictions on commercial use, AGT is the only option. BSL converts to a fully open licence after the change date, but until then, it has limitations that MIT does not.
For some organisations, especially those building products that embed governance components, this licensing difference is decisive.
You need multi-framework governance
If your agents run on LangChain, CrewAI, Google ADK, and Microsoft's own framework, AGT provides a single governance layer across all of them. Our platform is MCP-native and Claude-focused. If Claude is your primary model but not your only one, AGT's framework-agnostic approach covers more ground.
You want to contribute to an open-source project
AGT is genuinely open source. You can read every line of code, submit pull requests, and shape the project's direction. If your organisation values participating in the open-source governance ecosystem, and if having visibility into the governance layer's internals is a requirement, AGT provides that transparency.
There is also a strategic argument here. If AI agent governance becomes a regulated requirement (and the EU AI Act suggests it will), having your governance layer built on an open standard with community oversight is a defensible position. You are not dependent on a single vendor's interpretation of compliance. You can audit every policy evaluation path yourself.
When to Choose systemprompt.io
You need governance deployed in days, not months
The most common scenario I hear from CTOs: "We needed governance yesterday." Their teams are already using AI agents. The inconsistency, the lack of visibility, the compliance gaps are already causing problems. They cannot wait three months for a platform team to assemble components into a product.
systemprompt.io deploys in a day: binary, database, configuration. Your teams are onboarded by the end of the week. Governance policies are enforced from the first interaction. This is the fundamental advantage of a platform over a toolkit.
You need everything out of the box
Dashboard. User management. Cost tracking. Skill marketplace. SIEM integration. Audit trail. Analytics. If you need all of these (and most organisations do), building each one on top of AGT is a significant engineering commitment. Our platform includes all of them because they are core to what a governance product does.
The total cost of ownership calculation matters here. AGT is free, but engineering time is not. Building, testing, maintaining, and evolving a dashboard, user management system, and analytics layer on top of a toolkit has a real cost. For many organisations, that cost exceeds the price of a platform that includes everything.
You need air-gapped deployment
Some organisations cannot allow their governance infrastructure to communicate with the internet. Defence contractors, financial institutions, healthcare providers with strict data residency requirements. Our platform runs entirely on-premises with a single binary and a PostgreSQL database. No licence server calls, no telemetry, no external dependencies.
AGT can theoretically run air-gapped, but assembling all the dependencies, container images, and Azure service equivalents for an offline environment is a substantial effort. A single binary is a fundamentally simpler air-gap story.
You need skill and knowledge management
If your governance needs extend beyond policy enforcement to include managing what AI capabilities your teams have access to, how those capabilities are versioned and approved, and what knowledge bases they draw from, the marketplace and content management layers are core features. AGT does not address this layer at all. If you are still evaluating whether skills, agents, or plugins are the right abstraction for your organisation, the guide on plugins vs MCP servers vs skills breaks down the decision.
You need SIEM integration without building a pipeline
Connecting governance events to your SIEM should not be a project. Our three output paths (database, stdout, webhook) mean your security team can have governance events flowing into Splunk, Sentinel, or whatever they use within hours. With AGT, building that event pipeline is on your engineering team.
You are a smaller team
This is the scenario where the toolkit-vs-platform distinction is sharpest. A 50-person company with a 5-person engineering team cannot spare two engineers for three months to assemble governance infrastructure from components. They need something that works on Monday. That is the gap a complete product fills.
Can You Use Both?
This is a question worth asking seriously, because the two projects are not necessarily competing for the same layer.
AGT's strength is at the agent execution layer. Cryptographic identities, runtime sandboxing, and stateless policy evaluation are capabilities that operate close to the agent itself. The strength of the organisational governance layer we build is different. User management, skill governance, cost attribution, and SIEM integration are capabilities that operate across the entire AI deployment.
In theory, you could use AGT's Agent OS for runtime policy enforcement at the execution level, while using a complete platform for organisational governance, skill management, and observability. The MCP protocol could serve as the bridge: the platform governs what reaches the agent, and AGT governs what the agent does once it has the request.
In practice, this creates complexity. Two governance layers means two sets of policies to maintain, two audit trails to correlate, and two systems to monitor. For most organisations, the overlap in policy enforcement makes this more complicated than choosing one.
But for large enterprises with sophisticated platform teams and agents running across multiple frameworks, there is a real architecture here. AGT handles the multi-framework execution governance. The platform handles the organisational governance and human-facing layers. Each does what it does best.
Whether this combined architecture justifies the operational complexity depends entirely on your scale. Below a few hundred agents, it is almost certainly not worth it. Above a few thousand, across multiple frameworks and cloud providers, it starts to make sense.
There is also a temporal argument for using both. An organisation could deploy a complete platform today for immediate governance coverage, and begin building AGT-based components for specific execution-layer needs in parallel. Once the AGT components are production-ready, they slot in underneath the existing organisational governance layer. You get governance from day one without waiting for the custom build to complete.
I would not recommend this for most teams. The complexity cost is real. But I have seen organisations where different teams own different layers of the stack, and giving each team the tool that fits their mandate makes more sense than forcing everyone onto a single solution.
The Real Question: Build vs Deploy
Every toolkit-vs-platform comparison eventually reduces to the same question: does your organisation want to build governance infrastructure, or deploy it?
Microsoft AGT is a genuinely good toolkit. The engineering quality is high. The architecture is sound. The OWASP coverage is ambitious. If you have the team, the timeline, and the preference for owning every line of your governance stack, it gives you a strong foundation.
A complete product trades the flexibility of building your own for the speed of deploying something that works today. You get less control over the internals. You get more time to focus on what your organisation actually does.
Neither choice is wrong. But they serve different organisations with different constraints.
The question to ask is not "which is better?" It is: "Does my team have the capacity and the timeline to build governance infrastructure from components? And is that the best use of their time?"
If the answer is yes, and you genuinely have the engineering capacity to assemble, maintain, and evolve a custom governance stack, AGT gives you excellent building blocks with full source access and MIT licensing.
If the answer is no, and you need governance that works this week rather than this quarter, a complete platform removes the assembly step entirely. Your engineering team stays focused on your product. The governance infrastructure is someone else's maintenance burden. As the build-vs-buy guide covers in more detail, the AI landscape evolves too quickly for most organisations to maintain governance tooling alongside their core product.
There is a third answer that CTOs sometimes overlook: "not yet." Some organisations are early enough in their AI deployment that governance can wait. If you have five people using Claude casually, you do not need either AGT or systemprompt.io. You need a shared document with guidelines and a monthly check-in. Governance infrastructure becomes necessary when AI usage crosses the threshold from individual experimentation to organisational dependency. When decisions are being made based on AI outputs, when customer data flows through AI workflows, when consistency across teams starts to matter. That is when the toolkit-vs-platform question becomes urgent.
The arrival of Microsoft AGT in this space is a good thing regardless of which you choose. It validates that AI agent governance is infrastructure, not a feature. It raises the baseline for what governance should include. And it gives organisations a credible open-source option where none existed before.
The category is growing up. That benefits everyone building on AI agents, whether they choose a toolkit, a platform, or both.
Further Reading
- Awesome AI Agent Governance - A curated list of tools, frameworks, and standards for governing AI agents in production.